Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC)
The idea is to introduce a Role-Based Access Control (RBAC) to existing the users. Depending on your role in the organization, you will have different access permissions to resources across application. This is determined by an admin role user, who sets the parameters of what access a role should have, along with which users are assigned which roles. For instance, some users may be assigned to a role where they can write and edit particular files, whereas other users may be in a role restricted to reading files but not editing them. It’s possible for one user to be assigned multiple roles, giving them access to numerous different files or abilities
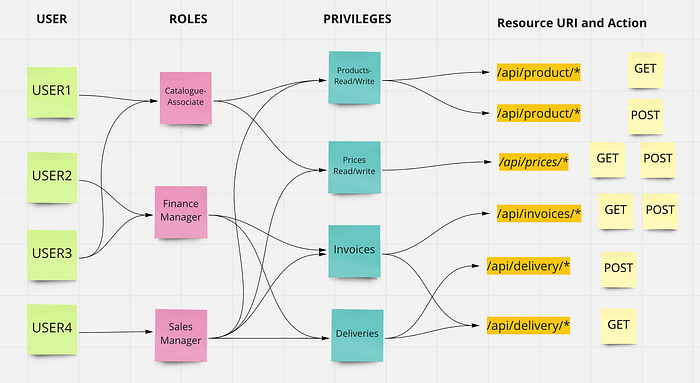
The aim is to assign a user specific role depending upon which it will have permissions to access API request assigned to the particular role. Few highlights from above example.
- USER1 has role of Catalogue Associate, which has privileges of Products Read/Write and Prices Read/Write so has access to all API request of product and prices.
- USER2 has role of Finance Manager which has privileges of Invoices and Deliveries, so has access to all API request of Invoices and Deliveries.
- USER3 has role of Catalogue Associate and Finance Manager which has privileges of Products Read/Write, Prices Read/Write, Invoices and Deliveries has access to resources under all the privileges.
- USER4 has admin who has all the privileges which gives it access to all resources.
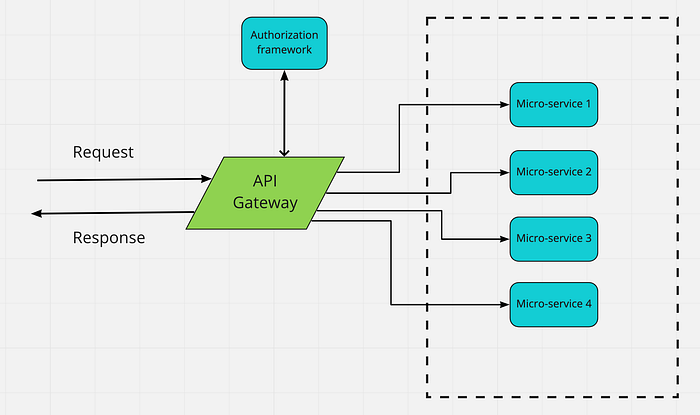
Implementation architecture
We will be introducing an API gateway which will be calling the Authorization framework. This Authorization framework will get the user form JWT token and get the access control for the role assigned to the user, based on the role assigned to the user it will allow/disallow the access of user to the resource before calling actual service. Authorization framework will be using Apache Shiro.
Apache Shiro Architecture
Apache Shiro is a powerful and easy-to-use Java security framework that performs authentication, authorization, cryptography, and session management. With Shiro’s easy-to-understand API, you can quickly and easily secure any application — from the smallest mobile applications to the largest web and enterprise applications.

- Subject : A security-specific ‘view’ of the entity (user) currently interacting with the software.
- Security Manager : Security Manager performs security operations and manages state for all application users. In Shiro’s default Security Manager implementations, this includes
Authorization,Session Management,Cache Management,Realm coordination,Event propagation,“Remember Me” Services,Subject creation,Logout and more - Authenticator : The Authenticator is the component that is responsible for executing and reacting to authentication (log-in) attempts by users. When a user tries to log-in, that logic is executed by the Authenticator. The Authenticator knows how to coordinate with one or more Realms that store relevant user/account information. The data obtained from these Realms is used to verify the user’s identity to guarantee the user really is who they say they are.
- Authorizer : The Authorizer is the component responsible determining users’ access control in the application. It is the mechanism that ultimately says if a user is allowed to do something or not. Like the Authenticator, the Authorizer also knows how to coordinate with multiple back-end data sources to access role and permission information. The Authorizer uses this information to determine exactly if a user is allowed to perform a given action.
- SessionManager : The SessionManager knows how to create and manage user Session lifecycles to provide a robust Session experience for users in all environments. By default, Shiro will use an existing session mechanism if available, (e.g. Servlet Container), but if there isn’t one, such as in a standalone application or non-web environment, it will use its built-in enterprise session management to offer the same programming experience
- CacheManager : The CacheManager creates and manages Cache instance lifecycles used by other Shiro components. Because Shiro can access many back-end data sources for authentication, authorization and session management, caching has always been a first-class architectural feature in the framework to improve performance while using these data sources
- Cryptography : Shiro’s crypto package contains easy-to-use and understand representations of crytographic Ciphers, Hashes (aka digests) and different codec implementations
- Realms : Realms act as the ‘bridge’ or ‘connector’ between Shiro and your application’s security data. When it comes time to actually interact with security-related data like user accounts to perform authentication (login) and authorization (access control), Shiro looks up many of these things from one or more Realms configured for an application. In this sense a Realm is essentially a security-specific DAO: it encapsulates connection details for data sources and makes the associated data available to Shiro as needed. When configuring Shiro, you must specify at least one Realm to use for authentication and/or authorization. The SecurityManager may be configured with multiple Realms, but at least one is required.
A Realm is a component that can access application-specific security data such as users, roles and permissions. The Realm translates this application-specific data into a format that Shiro understands so Shiro can in turn provide a single easy-to-understand subject programming API no matter how many data sources exist or how application-specific your data might be.
Realms usually have a 1-to-1 correlation with a data source such as a relational database, LDAP directory, file system, or other similar resource. As such, implementations of the Realm interface use data source-specific APIs to discover authorization data (roles, permissions, etc), such as JDBC, File IO, Hibernate or JPA, or any other Data Access API.
